XPI extensions
Firefox, Mozilla and Netscape 7.x versions based on them, use "Cross Platform Installable" files – abbreviated XPIs – to add extensions to the browser. They can be viewed and configured via the menu option "Tools/Extensions". The email program Thunderbird can also add on such XPI plug-ins.
XPI extensions are popular. The overview page of Mozilla.org lists more than 1,000 add-ons of all kinds. One of the reasons for this is, that they can be installed with just a few mouse clicks. You should, however, be aware that the installation executes programs that can, in principle, smuggle in spyware and dialers (see the Browsercheck XPI demo). Mozilla derivatives had been somewhat lax with this installation so that a hasty mouse click was often all it took to get infected.
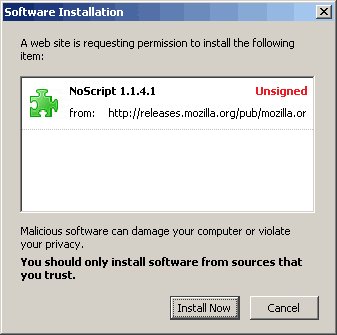
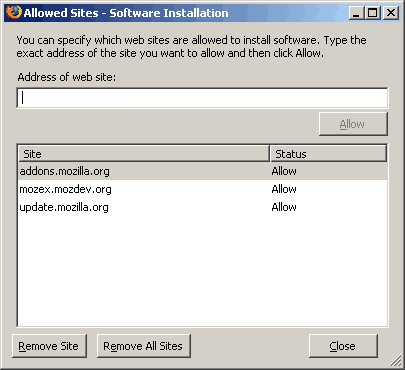
Mozilla 1.7 has added a two-stage warning for extra protection. First, the user of the site must enter the web site where the XPI came from to the list of sites that can install extensions locally. Before final installation, Firefox then gives the user five seconds to reconsider while a security warning is displayed. But the best protection is only to install add-ons from trusted sites, such as the download site of Mozilla.org.
XPIs can also be signed to provide users with reliable information about where the XPI came from. Unfortunately, the lack of infrastructure for this approach means that few extensions are actually signed in practice.









![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








