ActiveX
Your current setting:
| Launch of secure ActiveX controls |
| Launch of insecure ActiveX controls |
In Internet Explorer the ActiveX technology is used to add functionality – similar like plug-ins in the
Mozilla/Firefox/Netscape world. For example, ActiveX controls play multimedia files provided by the Web server in Internet Explorer. If the respective ActiveX control has already been installed on your computer, it will be launched by Windows and fed with data. The browser can also download the control automatically from the Internet.
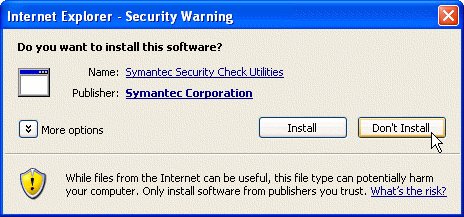
An ActiveX control can access any resources on the computer and thus is capable of inflicting any kind of damage. Internet Explorer distinguishes between signed and unsigned controls. A signed control is equipped with a digital signature by the vendor. An intact signature ensures that the control element has been created by the owner of the respective certificate and has not been modified since. This does not, however, mean that the ActiveX control cannot damage the computer. By default, Internet Explorer asks the user if signed ActiveX controls may be downloaded and installed; unsigned controls will not be downloaded.
ActiveX controls can also be enabled and controlled via JScript or VBS (as demonstrated in the test above). The security settings distinguish between controls that are "safe for scripting" and controls that are not. The vendor categorizes a control as "safe for scripting" if it is convinced that the control is harmless. However,
there have been cases where this assessment proved to be wrong. This risk should not be underestimated. If a Web page has installed an additional ActiveX control, for example, to perform a virus check on the computer, other, potentially malicious Web pages may also launch this control later and exploit any security issues therein.
ActiveX controls are often used to enhance the functional scope of Internet Explorer. For example, RealAudio or Quicktime players are enabled to play their multimedia files directly in the IE window. Although there are companies that offer services such as virus scans via ActiveX controls, the risk of potential abuse is quite high. Users who set value on security should therefore deactivate all ActiveX options or should at least activate the prompt setting.
Internet Explorer may also be used as an ActiveX control. For example, Outlook Express uses the IE control to display HTML mails, utilising the settings of the IE security zone selected under Outlook
Express.









![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








