iPhone OS 3.1.3 fixes vulnerabilities
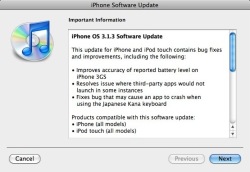
![]() The iPhone 3.1.3 update also addresses several security vulnerabilities.
Apple has released version 3.1.3 of its iPhone mobile operating system for all iPhone and iPod Touch devices to address a total of five vulnerabilities, some of which could be used to allow an attacker to take control of the device remotely. According to Apple, three of the vulnerabilities could allow an attacker to execute arbitrary code on a device. For an attack to be successful, a victim must first open a maliciously crafted MP4 audio file, TIFF image or access a specially crafted FTP server.
The iPhone 3.1.3 update also addresses several security vulnerabilities.
Apple has released version 3.1.3 of its iPhone mobile operating system for all iPhone and iPod Touch devices to address a total of five vulnerabilities, some of which could be used to allow an attacker to take control of the device remotely. According to Apple, three of the vulnerabilities could allow an attacker to execute arbitrary code on a device. For an attack to be successful, a victim must first open a maliciously crafted MP4 audio file, TIFF image or access a specially crafted FTP server.
Other vulnerabilities include a possible disclosure of information issue that could allow a person with physical access to a locked device to bypass the lock screen and gain access to a user's data and a problem that could cause Mail to load remote audio and video content when remote image loading is disabled. However, the update is not compatible with jailbroken devices and will disable the jailbreak and unofficial carrier unlocking. Users that have decided to jailbreak their devices are advised to wait for before installing the update.
The update is available to download via iTunes and weights in at around 300 MB. All users are advised to update as soon as possible. The iPod Touch update is priced £2.99 in the iTunes Store (iTunes Link) for users that have not yet upgraded to iPhone OS 3.x.
A recently discovered vulnerability involving the manipulation of certificates and configuration files, which can be exploited for man-in-the-middle attacks, has not been patched. The iPhone accepts configuration files (mobileconfig) for certain settings or even installation files with new certificates, provided that they are digitally signed. It doesn't seem to matter which Certificate Authority (CA) signs them, as long as it is a valid CA. Apple originally introduced the ability to distribute device configuration files using Over The Air (OTA) provisioning for enterprise users so that administrators could centrally manage a number of devices. Usually the validity of such files would be restricted to their own certificates.
Although victims to the exploit must first accept OTA mobileconfig files, with enough detail in the configuration file and certificate, odds are that they won't be suspicious of where such files come from. Using a malicious configuration file, an attacker could eavesdrop on a device and redirect all HTTP traffic from the phone to an arbitrary server on the net, allowing users to hijack SSL/HTTPS connections as well. All that an attacker needs to do is secretly enter a new HTTP proxy and enter their own SSL certificate into the list of certificates.
See also:
- About the security content of iPhone OS 3.1.3 and iPhone OS 3.1.3 for iPod touch, security advisory from Apple.
- iPhone PKI handling flaws, a Cryptopatch blog post.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








