Unsafe buttons in Google's toolbar
The Google Toolbar allows vendors and websites to install additional buttons, for example, to make it easier to search through their sites. However, security researcher Aviv Raff has discovered that an attacker can spoof information displayed during installation, both the origin of the button and the domain it exchanges information with. This simplifies attacks as criminals could use the button to conduct phishing attacks or persuade users to download and run programs from what they mistakenly believe is a trusted domain.
Attackers can fool the Google Toolbar by using a redirection, for example Google's publicly accessible redirector function, to enter a fake URL as the source for the installation files: http://www.google.com/local_url?q=. The Toolbar for Internet Explorer allows an attacker to fake the domains displayed under Downloaded from and Privacy considerations. In the Firefox version it is only possible to display a fake domain under Privacy considerations.
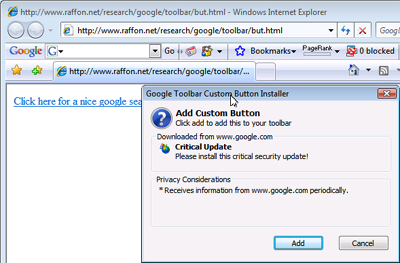
![]() Custom buttons in the Google Toolbar can conceal their provenance.
Custom buttons in the Google Toolbar can conceal their provenance.
Raff has provided a proof-of-concept on his server. If you click on the link you are asked if you want to install a button from Google containing data from the domain www.google.com. The button is actually from Raff's server, raffon.net. Once the button is installed and you click on it, you will download a file, although Internet Explorer will now show you the real domain hosting the file. However, a user who is not paying close attention at this point could easily download and install a trojan or similar.
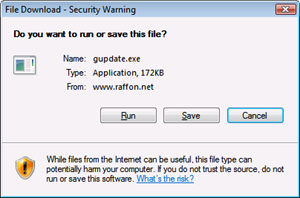
![]() IE shows the real address of downloads started by the button.
IE shows the real address of downloads started by the button.
Raff's security report states that Google has already been informed of the problem and is working on a fix. Until then, it is recommended that you avoid installing any new buttons in the toolbar.
- Google Toolbar Dialog Spoofing Vulnerability, security advisory by Aviv Raff
(mba)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








