Trojan construction kit for Mac OS X - yours for $1,000

![]() A Mac trojan is just clicks away.
A Mac trojan is just clicks away.
Source: Krebs on Security
According to security specialist Brian Krebs, in recent weeks a developer has been touting a trojan construction kit called Weyland-Yutani on underground forums; it enables criminals to construct malware for Mac OS X with just a few clicks. Construction kits of this type have previously only been available for Windows. The malware builder, which costs $1,000, generates malware for monitoring keystrokes that allows criminals to steal login credentials or credit card details – similar to the Windows trojans ZeuS and SpyEye.
Unlike on the Windows ecosystem, no exploit kits for Mac OS X are at present able to inject malware undetected onto a system via security vulnerabilities. The attacker always needs to persuade a victim to run an infected file, usually by means of social engineering, for example, on sites such as Facebook.
Weyland-Yutani hooks into Chrome and Firefox to monitor keystrokes entered into form fields. The developer told Krebs that he is also working on tapping into Safari, which comes preinstalled under Mac OS X. Like its Windows cousins, the Mac malware supports 'web injects' – addons which are able to modify web site content in real-time.
On top of this, Intego reports that in recent days a highly professional piece of scareware, MAC Defender, has been circulating. It is more than a match for well-known Windows counterparts, warning the user that their computer is infected and opening pornographic sites every couple of minutes to reinforce this impression.
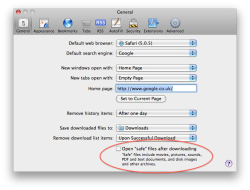
![]() To stop websites from running installation programs automatically, deactivate the "Open 'safe' files after downloading" checkbox.
The scareware program finds its way onto the user's computer as a zip archive as a result of a visit to a crafted web site. If a user is surfing with Safari, the download starts automatically and the installer contained within the archive is, by default, launched without user intervention. To stop this behaviour, users need to deactivate the checkbox under the Safari menu: Preferences, General, Open 'safe' files after downloading. The user is asked for their password before the scareware is installed.
To stop websites from running installation programs automatically, deactivate the "Open 'safe' files after downloading" checkbox.
The scareware program finds its way onto the user's computer as a zip archive as a result of a visit to a crafted web site. If a user is surfing with Safari, the download starts automatically and the installer contained within the archive is, by default, launched without user intervention. To stop this behaviour, users need to deactivate the checkbox under the Safari menu: Preferences, General, Open 'safe' files after downloading. The user is asked for their password before the scareware is installed.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








