Spanish police release details about Mariposa arrests
On Wednesday, the Spanish Guardia Civil police force released details about the arrest of three of the main suspects in connection with the "Mariposa" botnet![]() file. Three Spaniards, who have reportedly been arrested over the past few weeks, have been accused of having gained control of more than 13 million computers and of having operated one of the largest botnets worldwide since the end of 2008. According to the report, the authorities seized comprehensive evidence, such as the access data to corporate networks, online banking access credentials and email account details of more than 800,000 users in searches in Valmaseda, Santiago de Compostela and Molina de Segura.
file. Three Spaniards, who have reportedly been arrested over the past few weeks, have been accused of having gained control of more than 13 million computers and of having operated one of the largest botnets worldwide since the end of 2008. According to the report, the authorities seized comprehensive evidence, such as the access data to corporate networks, online banking access credentials and email account details of more than 800,000 users in searches in Valmaseda, Santiago de Compostela and Molina de Segura.
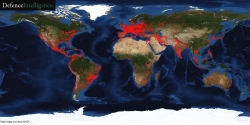
![]() Global distribution of the hijacked PCs in the Mariposa botnet.
Global distribution of the hijacked PCs in the Mariposa botnet.
Source: Defence Intelligence Team
The Guardia Civil's "Grupo de Delitos Telemáticos" was supported by the American FBI, the Georgia Tech Information Security Center, Spanish security software vendor Panda Security and the Defence Intelligence Team, which discovered "Mariposa" in May 2009 and subsequently identified numerous master servers that instructed hijacked Windows computers to download further malicious software, such as key loggers. The network appears to have been created predominantly by sending people links to specially crafted web pages via instant messages. When the receiver of such a message accessed one of these pages, an unspecified security hole in Internet Explorer was exploited to infect the computer.
The report says that the Mariposa botnet, whose "command and control server" was apparently already taken offline on the 23rd of December, involved computers in 190 countries, including PCs in schools, government institutions and hundreds of large corporations. The Guardia Civil is currently unable to quantify the damage caused. The botnet was apparently also rented out to other interested parties: For instance, the Defence Intelligence Team (whose own name was adulterated for master server domains such as "defintelsucks.com") registered massive DOS attacks on several Arab websites in early November. If sentenced in Spain, the Mariposa masterminds face several years in prison for computer sabotage and fraud.
(trk)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








