Serious security hole at ClickandBuy
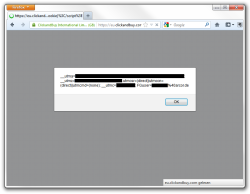
![]() The proof of concept enabled The H's associates at heise Security to steal the cookie of a logged-in user
A reader at heise Security – The H's associates in Germany – discovered a serious security hole in the web site of payment services provider ClickandBuy that allowed attackers to steal users' access data. The vulnerability in question is a cross-site scripting (XSS) hole that made it possible for attackers to inject arbitrary code into a ClickandBuy page due to insufficient parameter checks.
The proof of concept enabled The H's associates at heise Security to steal the cookie of a logged-in user
A reader at heise Security – The H's associates in Germany – discovered a serious security hole in the web site of payment services provider ClickandBuy that allowed attackers to steal users' access data. The vulnerability in question is a cross-site scripting (XSS) hole that made it possible for attackers to inject arbitrary code into a ClickandBuy page due to insufficient parameter checks.
For example, this enabled heise Security to transmit the cookie of a logged-in test user to an external server after the user had clicked on a specially crafted link to the page of the payment service. The reader had already informed the company of the problem in early July but had never received a reply. heise Security repeatedly contacted the company's press office and customer service department, but it took over a week before a spokeswoman for the Deutsche Telekom subsidiary responded and confirmed the problem. She expressed "deepest regrets" about the email having remained unanswered for so long.
The company told heise Security that the long response time was due to the message being incorrectly filed. ClickandBuy entrusts its system security to services such as McAfee Secure that are supposed to probe the site for vulnerabilities on a daily basis. However, the company said that due to a configuration error, the vulnerable page kept being omitted. According to ClickandBuy, there are no indications that the hole – closed on Tuesday 23 July – was actually exploited for an attack.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








