Scareware is getting down to business
![]() The Fakeinit scareware claims to be Security Essentials 2010.
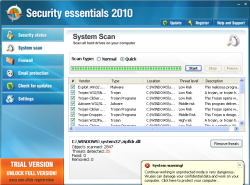
The Fakeinit scareware claims to be Security Essentials 2010.
Source: Microsoft
In its blog, the Microsoft Malware Protection Center (MMPC) describes a particularly stubborn type of scareware which calls itself "Security Essentials 2010", emulating the name of Microsoft's Security Essentials.
The scareware, labelled Fakeinit by Microsoft, doesn't just worry users by issuing dozens of fake virus and trojan alerts, it even actively gets down to business. Not only does it attempt to terminate various other programs, claiming they are infected, it also downloads and installs the Alureon root kit on the Windows PC.
Furthermore, the scareware inserts itself into the computer's network connection as a "Layered Service Provider" (LSP) component and monitors whether the user accesses specific pages. When a user tries to access popular websites such as amazon.com, ebay.com or twitter.com, Fakeinit blocks the connection and instead issues an infection alert in the browser – prompting the user to install anti-virus software.
Additionally, the scareware swaps the desktop background for the message "Your System is infected". Finally, it continuously opens the buy-security-essentials.com page and tries to coax the user into purchasing a full version of the "Security Essentials 2010" program for €50 (£45). The web page has since been taken off line.
Microsoft warns of Fakeinit, pointing out that the real Microsoft Security Essentials detect this scareware. However, the MMPC's blog does not give any practical instructions for users whose systems have already been infected. Suitable forums such as trojaner-board.de and xp-vista.com, on the other hand, offer various solutions. As the Alureon root kit is installed by the scareware, users should consider reinstalling their systems. Alureon recently attracted attention by causing blue screens after security update MS010-015 was installed under Windows XP.
See also:
- Microsoft confirms rootkit cause of Windows XP blue screen of death, a report from The H.
- Microsoft provides free Security Essentials anti-virus solution, a report from The H.
- Report: Phishing and scareware on the rise, a report from The H.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








