PayPal fixes critical vulnerability in its iPhone app

PayPal has released an update for its iPhone app aimed at blocking phishing attacks. According to a report in the Wall Street Journal, vulnerable versions of the app fail to check the PayPal web site's SSL certificate correctly, or at all. The Android app does not appear to be affected. The vulnerability was discovered by security company viaForensics.
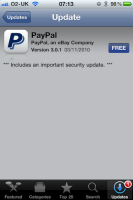
![]() PayPal users should update their iPhone app as soon as possible.
The vulnerability allows an attacker to reroute a victim's connection through his or her computer and to inject a fake certificate without the app raising an alarm. This would allow an attacker to view a victim's login details in plain text. As well as phishing attacks, the vulnerability can also be exploited to carry out sophisticated man-in-the-middle attacks. Modern browsers usually warn users when a certificate is incorrect – correct verification of SSL certificates is a fundamental element of secure online data transfer.
PayPal users should update their iPhone app as soon as possible.
The vulnerability allows an attacker to reroute a victim's connection through his or her computer and to inject a fake certificate without the app raising an alarm. This would allow an attacker to view a victim's login details in plain text. As well as phishing attacks, the vulnerability can also be exploited to carry out sophisticated man-in-the-middle attacks. Modern browsers usually warn users when a certificate is incorrect – correct verification of SSL certificates is a fundamental element of secure online data transfer.
The attack on the PayPal app only works in public (unsecured) Wi-Fi networks or Wi-Fi networks in which all users use the same key. The problem is not known to have resulted in any losses to date. Andrew Hoog, head of the analytical department at viaForensics described the bug to the Wall Street Journal as a "colossal oversight" by PayPal. The app is reported to have clocked up 4 million downloads. PayPal fixed the bug on Tuesday and has submitted the corrected version (3.0.1) to the Apple App Store.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








