Microsoft announces two-factor authentication
![]() The two-step verification asks for a second code during login – here, on iOS
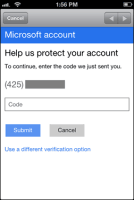
The two-step verification asks for a second code during login – here, on iOS
Source: Microsoft
In the next couple of days Microsoft plans to introduce an extension that will make the login process for Microsoft accounts more secure. The method, called "two-step verification" in a blog post, will require not only a conventional password, but also a code that the user gets by text message, email, or from a special app.
The Microsoft Authenticator app uses a standard protocol to create one-time codes that can also be used for services like Google and Dropbox. Microsoft does not specify in its announcement what that standard is, but it most likely uses time-based one-time passwords (TOTP), the generation of which is specified by the IETF in RFC 6238. Google's authenticator can therefore probably also be used to create TOTPs.
In fact, the details are very reminiscent of the two-factor authentication that Google introduced more than two years ago, especially the option to go through the two-step process only once on devices that are used often. And just like Google's method, there will be application-specific passwords for certain programs and services that don't support two-factor authentication.
Things could get tough if users find themselves unable to receive or generate the codes needed for the second step, for example if their smartphone is stolen. Without the second code, Microsoft says, users will have to wait 30 days before being able to access their account. In Google's system, users can generate special backup codes and keep them safe for such cases, a step which is recommended. Microsoft will most likely also include some kind of backup system at some point. If a user can't produce either of the two codes, they will simply lose access to their user account, according to the blog post.
According to the announcement, the new option will turn up in the next few days under "Security info" in the settings for each Microsoft account, although there is no clear information yet on whether Microsoft users in the UK are included in the immediate roll-out.
(fab)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








