Many SSDs and USB flash drives can't be securely wiped
Many solid state disks (SSDs), and other flash media such as USB flash drives and memory cards, cannot be securely wiped by software alone. Even after repeatedly overwriting the entire disk, traces of the original data may remain in the memory cells of NAND Flash chips. These traces cannot usually be accessed via the storage medium's standard interface, but they can be read directly from the chips using specialised electronics. According to a team of researchers from the University of California in San Diego led by Michael Wei, the lack of a reliable delete function makes this kind of medium unsuitable for certain usages.
The researchers presented their study![]() at the USENIX Conference on File and Storage Technologies (FAST'11). They experimented with a number of different SSDs and used a custom adaptor, based on an FPGA chip, to read individual flash chips which they had previously attempted to securely wipe using a range of different techniques. While some SSDs use the ATA secure erase command to achieve secure deletion, but not all do so and according to the research team, where it is used it is, in some cases, incorrectly implemented.
at the USENIX Conference on File and Storage Technologies (FAST'11). They experimented with a number of different SSDs and used a custom adaptor, based on an FPGA chip, to read individual flash chips which they had previously attempted to securely wipe using a range of different techniques. While some SSDs use the ATA secure erase command to achieve secure deletion, but not all do so and according to the research team, where it is used it is, in some cases, incorrectly implemented.
Repeatedly overwriting all data, considered a secure procedure for deleting data from magnetic disk drives, is not a reliable means of deleting data from SSDs – the use of wear levelling means that there is not a consistent relationship between physical (flash) memory cells and the sector addresses addressed by the device's normal (ATA / SATA / USB / SD) interface. Following deletion, deleted data is of course no longer accessible via this interface, but remnants can nonetheless remain on the individual chips. In contrast to standard hard drives, it is, according to the study, almost impossible to securely delete individual files on SSDs.
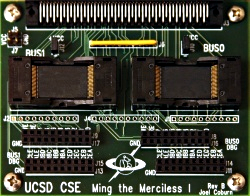
Ming the Merciless: FPGA adapter for reading individual NAND flash memory.
Source: UCSD
The researchers suggest that SSD manufacturers need to develop verifiable techniques for deleting data without leaving data remnants. They are talking not about wear levelling, but more generally about a flash translation layer (FTL) which generates the relationship between the logical block address (LBA) and the flash chip's physical 'pages'.
Special controllers on some recent hard disks and SSDs permit complete encryption of all data written to the drive with no loss of speed (full disk encryption, self-encrypting drive). This allows data to be securely deleted simply and quickly, merely by deleting the cryptographic key used to encrypt the drive. Wei's research group considers this procedure to be secure in principle, but, in view of the errors in implementation found in other methods of deletion, warns against being "unduly optimistic" in trusting in this solution.
Pitfalls also await software solutions such as TrueCrypt on SSDs. Firstly, retrospective encryption of partitions on media which make use of wear levelling can reduce the efficacy of encryption and impact on plausible deniability. Secondly, the write speed of SSDs can be reduced, since random numbers are written to free areas of memory so that it is not possible to tell how full a partition is.
For encryption functions built into hard drive controllers, the password can be entered using additional software, encryption can be controlled using a random value used as an ATA password, or the drive can be coupled to the motherboard's trusted platform module (TPM) via TCG Opal, so that it is only usable in conjunction with that motherboard.
Mechanical destruction of storage media, as used on normal hard drives, offers a reliable alternative means of destroying saved data.
(ehe)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








