Kaspersky says Stuxnet and Flame are related after all
 Anti-virus company Kaspersky has discovered a module that was originally developed as part of the Flame spyware, but was later used in one version of Stuxnet. Until now, virus researchers had found few similarities between the two super worms, other than that they were both deployed by secret service agencies.
Anti-virus company Kaspersky has discovered a module that was originally developed as part of the Flame spyware, but was later used in one version of Stuxnet. Until now, virus researchers had found few similarities between the two super worms, other than that they were both deployed by secret service agencies.
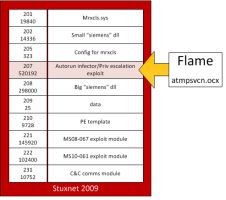
"Resource 207" is the internal name of a component from a 2009 version of Stuxnet. Its original purpose was to enable the virus to spread via USB flash drives, but it was later phased out. According to a Kaspersky blog posting, it is so closely related to Flame module atmpsvcn.ocx that virus analyst Alexander Gostev believes that the Stuxnet component was originally developed on the Flame platform, only later finding its way into Stuxnet.
![]() Stuxnet component "resource 207" was originally from Flame
Stuxnet component "resource 207" was originally from Flame
Source: Kaspersky
Following infection, "Resource 207" exploits a security vulnerability in win32k.sys, the Windows kernel, to obtain elevated privileges. When Stuxnet was first detected, this vulnerability was still undiscovered – it was a genuine zero day exploit.
Gostev speculates that there were two teams of developers with some sharing of information between the two teams, but they went their separate ways entirely around 2007 or 2008. The shared module was probably developed specifically for Stuxnet by the Flame team. This would explain why there is so little similarity between the two super worms. The blog post does not explore other explanations, such as that the exploits could have been purchased from third parties.
The New York Times has recently identified the US government – first under Bush, but continuing under Obama – as the driving force behind Stuxnet development and deployment. The newspaper claims that Obama in particular saw it as an effective method of disabling Iran's nuclear programme. Flame was also deployed primarily in Iran, but who was behind it remains a matter of speculation.
(djwm)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








