"Gauss" banking trojan probably government sponsored
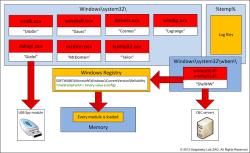
![]() The architecture of the Gauss trojan
The architecture of the Gauss trojan
Source: Securelist
During their investigation of the 20MB Flame "super spy" trojan, security researchers from Kaspersky Lab discovered a far more widespread cousin called "Gauss". The trojan is thought to have already infected tens of thousands of computers in Lebanon, Israel and Palestine.
Its malicious features include the theft of users' online account credentials including passwords, personal cookies, browser histories and other user-specific data. The malware also installs, for as yet unknown reasons, a custom font called "Palida Narrow". The name "Gauss" – most likely after the German mathematician Johann Carl Friedrich Gauss – was found in the malware's main module; various other modules are named after other famous mathematicians.
It is currently unclear which security hole or holes are exploited by Gauss to access the target systems. What researchers do know is that Gauss propagated via USB flash drives, exploiting the same security hole in the code for processing .LNK files that was previously exploited by Flame and Stuxnet. Gauss stored the harvested information on the flash drive in a hidden file.
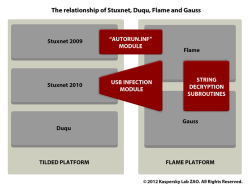
![]() The relationship between Stuxnet, Duqu, Flame and Gauss
The relationship between Stuxnet, Duqu, Flame and Gauss
Source: Securelist
The trojan is similar to the Flame super trojan in the composition and structure of its modules, in its code base, and in the way it accessed its command and control (C&C) servers. This gives rise to the assumption that they originated from the same source – Flame and Stuxnet have been attributed to secret services in Israel and in the US.
Against this background it seems particularly unusual that Gauss' spyware features targeted the online access data to users' bank accounts. Kaspersky notes that the trojan specifically looked for Bank of Beirut, Banque Libano-Française (EBLF), Blom Bank, Byblos Bank, Credit Libanais and Fransabank customer data. It is also believed to have intercepted Citibank and PayPal account access credentials.
Gauss was first sighted by Kaspersky in September 2011 and was identified as Trojan-Spy.Win32.Gauss in June 2012. The creators of the trojan soon became aware of the discovery: its C&C servers were taken offline in July; on infected systems, the trojan has been in hibernation mode since then. Kaspersky's Security Network (KSN) has counted more than 2,500 infections since May 2012 – however, this only includes systems that have Kaspersky products installed. In contrast, Kaspersky had counted only 700 Flame infections.
Like Duqu and Flame, Gauss features an auto-destruct mechanism – after 30 executions of the payload from a USB flash drive, the trojan will automatically delete itself to avoid being detected by anti-virus programs.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








