Allied Telesis – no backdoor in devices
![]() This "backdoor" caused quite a stir
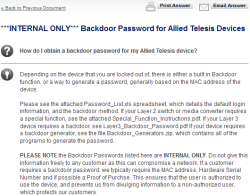
Allied Telesis denies charges that it has put backdoors into all of its products. Recently, the Japanese manufacturer of network equipment accidentally published an internal support document containing information about a "backdoor password for Allied Telesis devices." Now, the company says the description is misleading and that the tools it published merely serve to reset the administrator password, which it says is a common function.
This "backdoor" caused quite a stir
Allied Telesis denies charges that it has put backdoors into all of its products. Recently, the Japanese manufacturer of network equipment accidentally published an internal support document containing information about a "backdoor password for Allied Telesis devices." Now, the company says the description is misleading and that the tools it published merely serve to reset the administrator password, which it says is a common function.
Allied Telesis says that customers primarily contact their support teams to get access to blocked devices following staff changes or when they purchase used hardware. The company does not see any security risks, pointing out that users still need to know the correct MAC address and serial number before they can use the tool to access a device's serial interface. Furthermore, the tools that were made public allegedly only work with old firmware versions that are no longer used.
The released document was never intended for the public; a staff member accidentally put the document into the support area on the company's web site. The firm has since removed the information from the support page and is trying to prevent it from being circulated elsewhere – which will be a difficult task.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








