Aldi PC becomes first retail PC with UEFI Secure Boot

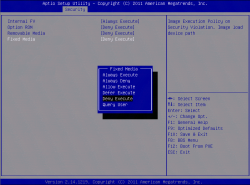
![]() UEFI Secure Boot can only be activated on the MS 7800 motherboard once administrator and user passwords have been set
UEFI Secure Boot can only be activated on the MS 7800 motherboard once administrator and user passwords have been set
The first systems to support UEFI Secure Boot, which is a requirement for carrying the Windows 8 logo, have now been released. The requirements have been controversial for open source operating system makers as they have attempted to work out how to work with the Secure Boot and Microsoft's demands for logo compliance, especially as no systems were available with Secure Boot implemented. Compatible UEFI firmware contains a platform key (PK), a key exchange key (KEK) and two signature databases for checking signed code prior to execution. As defined in the UEFI 2.3.1 specification, which is being commercially implemented in Windows 8 for the first time, Secure Boot is intended to prevent malware from running before the operating system has booted.
Aldi is now selling the Medion Akoya P4210 D (also sold under the model number MD 8370) which is one of the first systems to include motherboard firmware which supports UEFI Secure Boot. The BIOS setup (or rather UEFI setup) includes three menu pages for setting up Secure Boot options and for key management. As required by Microsoft for standard desktop computers bearing the Windows 8 logo, Secure Boot can be disabled. It is also possible to add additional key exchange keys and signatures.
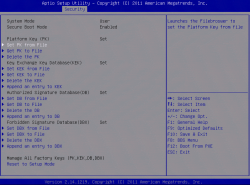
![]() The decision on whether an executable file should be executed when a signature test identifies a rule breach is location-dependent (hard drive, removable media, optical media, etc.), with different user settings for each location
The decision on whether an executable file should be executed when a signature test identifies a rule breach is location-dependent (hard drive, removable media, optical media, etc.), with different user settings for each location
The system is based on MSI's MS 7800 motherboard (an OEM product designed for Medion which has Secure Boot turned off by default. The UEFI specification calls this configuration "Setup Mode" and the system has to be switched to "User Mode", which loads the relevant keys and databases, in order to enable Secure Boot. In User Mode, the system requires an administrator and a user password to be set in order to restrict access to Setup Mode. To improve security, these passwords have certain restrictions placed on them in the MS 7800's implementation as they must include upper- and lower-case letters and other variations. If both passwords are set, users can configure Secure Boot to prevent "insecure" UEFI applications and bootloaders from being executed.
Under Windows, Secure Boot can only be used in conjunction with Windows 8's UEFI mode. For those Windows 8 versions which are user installable, this means users have to use the 64-bit version of the operating system and that the hard drive containing the system partition must contain a GUID partition table (GPT). Users wanting to install a 32-bit version of Windows or a 64-bit version in BIOS mode will have to disable Secure Boot. Depending on the firmware, it may be possible to switch this function on and off at boot time as required, though it is not clear how well this will work with features like "suspend to RAM" or "wake on LAN".
![]() The UEFI 2.3.1 firmware manages key and signature databases to which items can be added by the user
The UEFI 2.3.1 firmware manages key and signature databases to which items can be added by the user
UEFI Secure Boot does not require a Trusted Platform Module (TPM) – Microsoft only requires this for tablets containing ARM or Atom SoCs and which support "connected standby" functionality. Secure Boot cannot be disabled on ARM systems with Windows RT, but can be disabled on connected-standby-enabled tablets running x86 SoCs – this most likely results in the loss of connected standby functionality, however. Several Linux distributions are also planning to support Secure Boot, but have different means of achieving this.
Update 18-07-12: An earlier version of this article misstated the steps needed to activate Secure Boot and which passwords need to be set in the UEFI firmware to enable it.
See also:
- The FSF weighs in on UEFI Secure Boot, a report from The H.
- Canonical details Ubuntu UEFI Secure Boot plans, a report from The H.
- Fedora 18 to support UEFI Secure Boot, a report from The H.
(fab)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








