64-bit rootkit spies on online banking customers
![]() Unexpected helper: Microsoft's bcdedit.exe tool enables the rootkit to bypass the Kernel Patch Protection feature of 64-bit Windows systems.
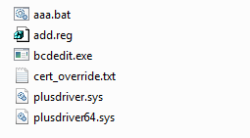
Unexpected helper: Microsoft's bcdedit.exe tool enables the rootkit to bypass the Kernel Patch Protection feature of 64-bit Windows systems.
Source: Kaspersky Lab
Security specialist Kaspersky has discovered another rootkit with 64-bit Windows support: a variant of the Banker rootkit is targeting the access credentials of online banking customers in Brazil. The malware is injected into systems via a hole in an obsolete version of Java and first disables the Windows User Account Control (UAC) feature so that it can go about its business without being interrupted. It then installs bogus root certificates and modifies the HOSTS file in such a way that victims trying to access the banking web site are redirected to a phishing site operated by the criminals. The injected certificate prevents the browser from issuing an alert when establishing an encrypted connection to the phishing site, and the victim is left unaware. Kaspersky says that the malware also deletes a security plug-in used by various Brazilian banks.
Unusually, the malware installs a custom system driver to uninstall the security plug-in and modify the HOSTS file. On 64-bit Windows systems, this requires some effort because Microsoft's Kernel Patch Protection (PatchGuard) prevents unsigned drivers from being installed. As 64-bit Windows installations still have a relatively small market share, rootkits with 64-bit support are currently still quite rare; a 64-bit version of the Alureon/TDL rootkit was discovered last November.
Similar to Alureon, Banker uses a test mode that is actually intended to enable developers to bypass PatchGuard: the malware uses Microsoft's bcdedit.exe tool to enable the TESTSIGNING option, which makes Windows accept the test certificate for the rootkit's plusdriver64.sys driver. Microsoft originally implemented the Windows TESTSIGNING mode as an option for developers who wish to test their custom drivers on a 64-bit system before the drivers have officially been signed. The option has been part of the 64-bit versions of Windows since Vista.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








