.lnk vulnerability in Windows: Attack wave approaches
![]() The critical vulnerability in the code for processing short-cuts (.lnk files) in all versions of Windows remains unpatched, attracting a growing number of exploits. At least two further malicious programs are now targeting the vulnerability, and the number of undetected cases is likely to be much higher. While the first .lnk trojan, Stuxnet, appeared to be the result of professional industrial espionage, new worms are not as selective in terms of their targets.
The critical vulnerability in the code for processing short-cuts (.lnk files) in all versions of Windows remains unpatched, attracting a growing number of exploits. At least two further malicious programs are now targeting the vulnerability, and the number of undetected cases is likely to be much higher. While the first .lnk trojan, Stuxnet, appeared to be the result of professional industrial espionage, new worms are not as selective in terms of their targets.
Security firm ESET has observed the Win32/TrojanDownloader.Chymine.A malware in the wild. This malware contacts a server in the US and downloads the Win32/Spy.Agent.NSO key logger from there. The Win32/Autorun.VB.RP worm is now also said to have discovered the .lnk hole as a suitable means for propagation. The worm even actively produces further compromised .lnk files so it can spread faster.
The full scope of the problem is yet unknown. What is known is the at all versions of Windows from XP onwards are affected. A few days ago, Microsoft added that specially crafted short-cuts for executing malicious code can also be embedded in Office documents. Furthermore, .lnk files are not the only file type affected: According to Microsoft's updated advisory, PIFs (Program Information Files) are also vulnerable. Core Security said it had` found a way of exploiting the hole via emails, although the security firm hasn't provided any details.
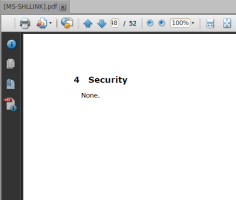
![]() Page 48 of the official documentation for the LNK format.
Page 48 of the official documentation for the LNK format.
Source: The H Security
Even the German Federal Office for Security in Information Technology (BSI) has issued a warning (German language link): until the hole has been patched users are to follow the steps for the work around described in Microsoft's security advisory. Microsoft's fix-it is indeed the easiest way to protect a system from impending attacks. However, it does cause a loss of convenience, as Windows will only display standard icons for all short-cuts once the fix-it has been applied.
Incidentally, Microsoft has removed the official documentation for the .lnk file format ("[MS-SHLLINK]: Shell Link (.lnk) Binary File Format") from its server without comment. Critics sneer that this was done to remove the description of the format's security measures on page 48 (see screen-shot above).
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








