VLC Media Player 1.1.3 fixes critical security vulnerability
![]() The VideoLAN Project release team have announced arrival of version 1.1.3 of their VLC Media Player, a free open source cross-platform multimedia player for various audio and video formats. According to the developers, the latest maintenance and security update fixes several bugs across all platforms.
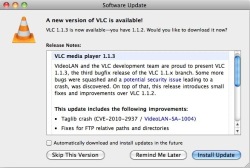
The VideoLAN Project release team have announced arrival of version 1.1.3 of their VLC Media Player, a free open source cross-platform multimedia player for various audio and video formats. According to the developers, the latest maintenance and security update fixes several bugs across all platforms.
The update eliminates a critical security vulnerability (CVE-2010-2937) within the TagLib plug-in that results in a memory corruption error when extracting meta-data from ID3v2 tags. The vulnerability, reported by security specialist FortiGuard Labs, could be used to crash the player, possibly resulting in a denial of service (DoS) attack or potentially leading to the execution of arbitrary code. For such an attack to succeed the victim would first have to download and open a specially crafted file – for example a video file from a manipulated file hosting service. Users are reminded not to open files from untrusted third parties or untrusted remote web sites. Versions 0.9.0 to 1.1.2 of the VLC Media Player are reportedly affected.
Other changes include various extension and script updates, fixes for the Podcast and DVD modules, and a number of updated translations. The developers advise all users to upgrade to the 1.1.3 release as soon as possible.
More details about the release can be found in the release announcement, in the change log and on the What's new in 1.1.3 page. VLC 1.1.3 is available to download either as source or as binaries for Windows, Mac OS X and Linux. Users that already have VLC installed can use the built-in update tool. VLC is released under version 2 of the GNU General Public License (GPLv2).
See also:
- Insufficient input validation in VLC TagLib plugin, security advisory from the VideoLAN Project.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








