URI problem also affects Acrobat Reader and Netscape
After being notified by heise Security, Skype silently fixed a security problem in the handling of special URLs by releasing an updated version 3.5.0.239. Other programs such as Adobe's Acrobat Reader, the Netscape browser, and the Miranda Instant Messenger still launch arbitrary programs when special URLs containing the % character are clicked on. In doing so, they may allow spyware to be installed on the user's system. The developers of Mozilla have at least temporarily remedied a similar problem in Firefox.
The Mozilla team categorized the vulnerability as critical, released a dedicated security advisory, and provided users with a patched version via the update function. In contrast, Skype just published a minor update and mentioned "bugfix: Links with invalid % encodings were executed" in the Release Notes, which normal users will never see. Skype users are therefore advised to install the latest version by themselfs. The procedure is quite simple: simply click on "Help/Check for updates".
One could spend all day debating whether Skype is ultimately responsible for the problem or whether Windows is. Jüri Shamov-Liiver, head of product security for Skype, for instance stated in a discussion with heise Security: "Basically it is a Windows flaw." He argues that Skype merely passes the URL on to the operating system. And there is no denying that Microsoft changed the handling of URLs by the operating system with the installation of Internet Explorer 7 for Windows XP. As a result, special links containing the % character can cause arbitrary programs to be launched.
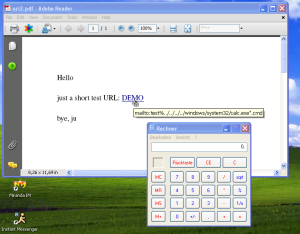
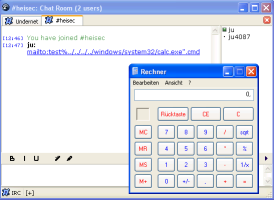
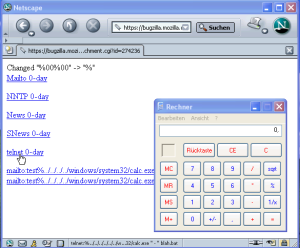
While Skype and Firefox have added additional filters to remedy the problem, it has not been remedied once and for all. Theoretically, any application not made by Microsoft that passes URLs on to Windows can be vulnerable because it does not take in account the changes made by installing IE 7. In fact a small sample survey conducted by heise Security found, that for instance Adobe's current Acrobat Reader could also be practically exploited as a way of injecting contaminants: we managed to launch the calculator by clicking on a link in a specially crafted PDF file. Furthermore, the current Netscape browser and the recently released version 0.7 of the Miranda Instant Messenger also proved to be vulnerable – and the list could probably be extended further.
As yet, Microsoft does not see any reason to react. After contacting the Microsoft Security Response Team on this issue, we received the reply:
"After its thorough investigation, Microsoft has revealed that this is not a vulnerability in a Microsoft product."
In other words, a large number of Windows XP users being affected by a serious security problem, which only occurs if they install Internet Explorer 7 and is not present at all in Vista, is not sufficient to justify an update. Microsoft prefers to sit back and watch while users and application developers struggle to secure Windows XP systems that behaved perfectly before IE7 was installed.
Update:
The problem is not restricted to mailto:-URLs. In fact, even entering
http:%xx../../../../../../../../../../../windows/system32/calc.exe".bat
under "Start/Run" launches the calculator. And according to a report on the security mailing list Bugtraq the IRC client mIRC is affected as well.
Update 2:
It is possible to specify "Open a web link" as action to perform when a PDF is opened in a viewer. This means, that it is enough to open an evil PDF file in Acrobat Reader to execute arbitrary programms and possibly infect a system with spyware. A demo PDF constructed by heise Security launched the calculator when it was opened without any further user interaction. This critical security problem is propably the same as recently detected and described by Petko Petkov.
- Skype also affected by supposed "Firefox vulnerability" report by heise Security
- New version of Firefox with security fix for URI vulnerability report by heise Security
(mba)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








