Trustwave issued a man-in-the-middle certificate
![]() All of the major browsers contain the Trustwave root certificate
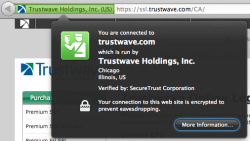
All of the major browsers contain the Trustwave root certificate
Certificate authority Trustwave issued a certificate to a company allowing it to issue valid certificates for any server. This enabled the company to listen in on encrypted traffic sent and received by its staff using services such as Google and Hotmail. Trustwave has since revoked the CA certificate and vowed to refrain from issuing such certificates in future.
According to Trustwave, the CA certificate was used in a data loss prevention (DLP) system, intended to prevent confidential information such as company secrets from escaping. The DLP system monitored encrypted connections by acting as a man-in-the-middle, meaning that it tapped into the connection and fooled the browser or email client into thinking it was communicating with the intended server. To prevent certificate errors, the DLP system needed to be able to produce a valid certificate for each connection – the Trustwave CA certificate enabled it to issue such certificates itself. The same principle is utilised by espionage attacks and government monitoring activities.
The usual procedure for legitimate data loss prevention is for administrators to set up an internal certificate authority which, in consultation with staff and management representatives, is then installed on work devices. Such a system is not, however, able to offer protection where staff are using personal devices which do not belong to the company.
Trustwave is keen to point out that the company to which the certificate was issued had signed a usage agreement and both the secret CA key and the fake certificates generated using it were securely stored in a specially tested hardware security module (HSM). According to Trustwave, this meant that it was impossible to misuse the certificate for nefarious purposes. The company has nonetheless decided that it will not be pursuing this business avenue in future. The certificate has been revoked and Trustwave says that it will not be issuing any further certificates of this nature.
Security experts and privacy advocates have been warning for a while that any CA and any sub-CA authorised by it are able to issue certificates for any server. This is a cause of particular concern in the case of some government CAs, where there is every likelihood that they could assist with monitoring activities. This is the first case that we are aware of where a respectable certificate authority has enabled third parties to issue arbitrary SSL server certificates for monitoring purposes. Trustwave claims, however, that this is common practice among other root CAs.
(ehe)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








