Tell-tale status pages
 Many web servers, including those of banks, porn sites and other types of online portals, publish their users' security or privacy-related information on status pages that are publicly available. The problem is caused by the originally harmless mod_status Apache module – or rather by the careless way in which many administrators handle this useful tool.
Many web servers, including those of banks, porn sites and other types of online portals, publish their users' security or privacy-related information on status pages that are publicly available. The problem is caused by the originally harmless mod_status Apache module – or rather by the careless way in which many administrators handle this useful tool.
The module uses the /server-status page to present system load information that includes currently active connections – complete with clients' URLs and IP addresses. This information is useful to the administrator, but it could become a problem in the wrong hands. If, for example, an adult web site publishes the user-specific IP addresses of livegranny.com customers, or German courier company Deutsche Post at least partially discloses the session IDs of its Postpay![]() payment service transactions that have just been completed, it becomes clear that this information is definitely worth protecting.
payment service transactions that have just been completed, it becomes clear that this information is definitely worth protecting.
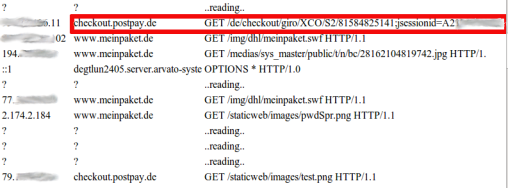
![]() A payment processing service's session ID is definitely worth protecting as it allows attackers to hijack a logged-in user's session
A payment processing service's session ID is definitely worth protecting as it allows attackers to hijack a logged-in user's session
Still, hundreds of servers make this information freely available to anyone and easily found using search engines. Shortly after the problem became known, Santander bank blocked the access to its status page; however, at least one German bank has yet to react to the issue. Even seemingly harmless information may disclose path, server name or parameters that can potentially be useful for the preparation of an attack. Security-conscious administrators should, therefore, at least restrict the access to such information to specific IP addresses or request that visitors authenticate themselves.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








