Source code for the Zemra crimeware bot released - Update
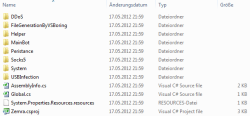
![]() Bot component set - the Zemra source code can be used to construct troublesome bots
Source code for the Zemra trojan, which is already being used by criminals for distributed denial-of-service (DDoS) attacks, is currently circulating online. In contrast to the widely distributed Zeus bot, the source for which is also available online, Zemra is very new. According to security company Symantec, it has only been available to purchase from underground forums since May this year and malicious parties are currently using it against organisations for the purpose of extortion. Disturbingly, Symantec's own anti-virus solutions have only been able to detect it for about a week now.
Bot component set - the Zemra source code can be used to construct troublesome bots
Source code for the Zemra trojan, which is already being used by criminals for distributed denial-of-service (DDoS) attacks, is currently circulating online. In contrast to the widely distributed Zeus bot, the source for which is also available online, Zemra is very new. According to security company Symantec, it has only been available to purchase from underground forums since May this year and malicious parties are currently using it against organisations for the purpose of extortion. Disturbingly, Symantec's own anti-virus solutions have only been able to detect it for about a week now.
Symantec says that the crimeware pack is not currently very widespread. However, the availability of the source code means that this could rapidly change, since anyone can now modify the bot for their own ends. This is not especially hard – Zemra was developed using the C# programming language. The source code should be comprehensible to anyone with basic programming skills, and new functionality can be added with relative ease.

![]() Source code for the PHP-based Zemra command and control sever is also included in the archive
Source code for the PHP-based Zemra command and control sever is also included in the archive
Source: Symantec
Most fraudsters are likely to be more than happy with just the basic version, however. As well as various types of DDoS attack, Zemra can also download and run malicious programs from the web on command. It can also open a SOCKS proxy on an infected computer, allowing the bot herder to utilise the victim's internet connection for whatever purposes he wishes. Zemra is also able to spread via USB flash drives. Communication between the bot and the PHP-based command-and-control server (also supplied) is encrypted.
Update 04-07-12: In a conversation with The H's associates at heise Security, the person responsible for the easysurfer.me![]() blog has declared that they have leaked the source code for the bot. They claim to have changed it, before releasing it, in such a way that so that it is not easily compiled. In a blog posting
blog has declared that they have leaked the source code for the bot. They claim to have changed it, before releasing it, in such a way that so that it is not easily compiled. In a blog posting![]() , they have analysed the important portions of the source and are pointing out a backdoor in the command server.
, they have analysed the important portions of the source and are pointing out a backdoor in the command server.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








