Security hole in Internet Explorer allows attackers to execute arbitrary programs
Aviv Raff has discovered that arbitrary programs can be executed when crafted web pages are printed in Internet Explorer. The vulnerability is based on a cross-zone scripting hole allowing web pages to execute code in the local zone instead of the internet zone. However, user intervention is required.
Raff has created a sample page to demonstrate the hole. The web page calls the Windows computer if the user prints it using the "Print Table of Links" feature. It is irrelevant whether the user allows the execution of active content as warned by IE. heise Security was able to reproduce the behaviour in Windows XP SP2 with all current patches and Internet Explorer 7.
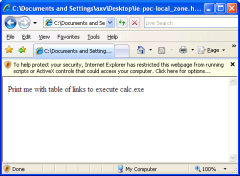
![]() Although IE issues a warning before executing active content, it can be executed silently when printing link tables.
Although IE issues a warning before executing active content, it can be executed silently when printing link tables.
When users print a page in IE, the browser uses a local script which generates a new HTML file to be printed, explains Raff. The HTML contains a header, the web page body, a footer – and, if enabled, also the table of links in the web page. However, the script does not check the URLs contained in the links, adding them to the new HTML file as presented without any filtering. In Internet Explorer, most local scripts run in the internet zone, but the printing script runs in the Local Machine Zone. This opens up the security hole, allowing any injected JavaScript to execute arbitrary code on the user’s machine. By embedding specially crafted links in a web page, and with a little social engineering to get visitors to print the page containing the link table, attackers can therefore inject arbitrary code on users' computers. According to Raff, the vulnerability affects not only IE 7 but also the beta version of IE 8.
While the vulnerability allows code to be executed under Windows XP, Windows Vista with activated User Account Control (UAC) only allows attackers to spy out information, explains Raff. Older versions may also be affected by the problem. Users are advised to refrain from printing web pages with link tables until Microsoft has released a patch.
See also:
- Internet Explorer "Print Table of Links" Cross-Zone Scripting Vulnerability, demonstration of the vulnerability in the milw0rm archive
(mba)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








