Report: DDoS service as a legitimate, FBI-approved business

US security blogger Brian Krebs writes about a service that is relatively new, at least to the general public: DDoS attacks. Apparently, one enterprising "stress tester" discovered by Krebs even told the blogger that he was working for the FBI.
The "booters" market their services to the public, thinly disguised as facilities that allow administrators to stress-test their own systems. Krebs says that he located and interviewed one of them, a 22-year-old US citizen. The booter told him that he considered his DDoS testing to be perfectly legal. Individuals used it at their own risk and on their own responsibility, he said in a response that was riddled with spelling and grammatical mistakes. The booter explained that, for scenarios such as DNS amplification attacks, his service merely took advantage of many DNS servers' default settings. If server operators didn't agree they could prevent it, he told Krebs.
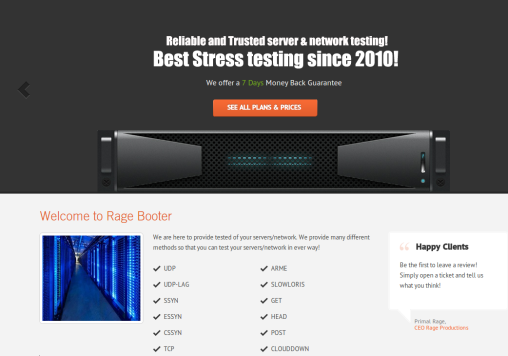
![]() The "booters" publicly market their attacks as stress tests
The "booters" publicly market their attacks as stress tests
The booter went on to explain that he even works for the FBI. Reportedly, the FBI allows him to continue his business and receives full access to the log files of all customer activities in return. By way of proof, he provided the alleged details of his FBI contact. When Krebs called the number and disclosed that he was a journalist, he wasn't given any information on the matter. However, only minutes after the conversation with the FBI, the booter cut his contact to Krebs, saying: "I have been asked to block you. Have a nice day."
A former Washington Post journalist, Krebs has earned an excellent reputation as a security blogger based mainly on his exposure of activities in the cyber underworld. His article is credible, although attacks on third-party services do violate applicable laws in almost all countries. For this reason, serious pen testers are sure to check very carefully whether their customers actually have the right to authorise such an attack.
(fab)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








