QuickTime pickpocketing in Second Life
Linden Lab, the company that operates the Second Life online world, has warned players of the consequences of a recently discovered vulnerability in QuickTime, which is already being exploited in the wild on a number of malicious web pages. The Apple video framework is used to play embedded video sequences in the virtual game world. According to a MercuryNews.com report, security experts have already succeeded in creating a manipulated video clip that can extract 12 Linden dollars (approximately 4,5 US cents) from the pocket of avatars in the range of an object embedding the malicious video, while forcing them to say, “I got hacked.”
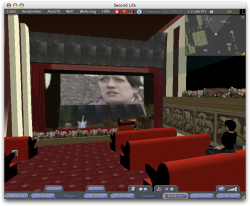
![]() Video content is available in Second Life on any server corner. Some of it is even played automatically with the default settings.
Video content has become a widespread feature among virtual corporate presences, businesses and cinemas in Second Life. Even tutorials are often created in the form of short QuickTime film clips. The Second Life client, in its default setting, automatically plays some video content in the avatar environment.
Video content is available in Second Life on any server corner. Some of it is even played automatically with the default settings.
Video content has become a widespread feature among virtual corporate presences, businesses and cinemas in Second Life. Even tutorials are often created in the form of short QuickTime film clips. The Second Life client, in its default setting, automatically plays some video content in the avatar environment.
The operators of Second Life acknowledge that they could temporarily deactivate all video content in their virtual game world, but are hesitant to do this out of regard for legitimate streaming content. They point out that it is always possible to discover users offering malicious video streams and pursue legal avenues against them if necessary.
Linden Lab explicitly recommends deactivating video streaming in the Second Life clients, however, until a security patch for QuickTime is available and to allow only videos in trusted game world regions as needed. This option can be found under Preferences / Audio & Video / Play Streaming Video When Available.
See also:
- Web pages infect PCs via Apple QuickTime vulnerability , security alert by heise Security
- Second Life Viewer Susceptible to Quicktime Security Flaw, Linden Lab blog entry
- Second Life pickpockets threaten real world cash potential, MercuryNews.com report
(mba)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








