Privacy for RFID tags
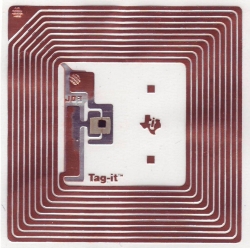
![]() A Texas Instruments RFID tag
A common complaint about proposals to use RFID (Radio Frequency Identity) to tag everything from bank notes to underwear is that it opens the way for sophisticated privacy invasion. Someone with a reader could, once RFID is pervasive, read the valuables you're carrying, the contents of your wallet, and plan an attack accordingly. The solution so far: a kill function to disable the tags at the point of sale.
A Texas Instruments RFID tag
A common complaint about proposals to use RFID (Radio Frequency Identity) to tag everything from bank notes to underwear is that it opens the way for sophisticated privacy invasion. Someone with a reader could, once RFID is pervasive, read the valuables you're carrying, the contents of your wallet, and plan an attack accordingly. The solution so far: a kill function to disable the tags at the point of sale.
Speaking at this week's Enisa-Forth Summer School on Network Information and Security, RSA chief scientist Ari Juels noted problems with the kill function, mostly to do with key management: "Cryptography is not hard; managing privileges is hard."
Juels' idea – which he worked on with colleagues Bryan Parno and Ravi Puppu – is instead to share a secret key across a group of tags. For example, split the key across the RFID tags on each of a set of bottles. A pharmacy taking delivery can check and store the keys transparently. "You can reconstruct the key when the bottles are together," he explained. "But when the bottles are dispersed, the key essentially vanishes. You have automatic privacy protection. Plus, no kill function – and no key management burden through the supply chain."
One problem is that this system invalidates one of the promises usually made about using RFID tags; users will be able to check the tags themselves as an anti-counterfeiting measure. Juels admits that's true, but says there are alternative solutions to that. "Treating the fundamental privacy problem is so challenging that more sophisticated functions will have to wait."
In other recent work, Juels and colleagues cloned a State of Washington electronic driver's licence and showed it could be read at a range of more than 50 metres under experimental conditions – and at 0.5 metres in the State-supplied protective sleeve.
(Wendy M. Grossman)
(trk)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








