Password leaks bigger than first thought
![]() The published password hashes do not contain any email addresses or usernames
There have still been no official statements on the causes and extent of the recent password leaks at LinkedIn, eHarmony and Last.fm. A credible source is now reporting that the published 2.5 million Last.fm MD5 hashes, for example, are just the tip of a 17 million hash iceberg. That iceberg has reportedly been circulating since summer 2011.16.4 million of these â 95 per cent â have, the source claims, already been cracked, a claim which, for unsalted hashes, is entirely credible.
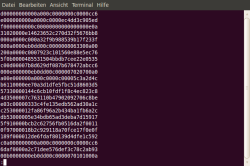
The published password hashes do not contain any email addresses or usernames
There have still been no official statements on the causes and extent of the recent password leaks at LinkedIn, eHarmony and Last.fm. A credible source is now reporting that the published 2.5 million Last.fm MD5 hashes, for example, are just the tip of a 17 million hash iceberg. That iceberg has reportedly been circulating since summer 2011.16.4 million of these â 95 per cent â have, the source claims, already been cracked, a claim which, for unsalted hashes, is entirely credible.
Since the lists do not contain any duplicates, it is likely that the number of affected users is in fact much larger than originally thought. Similarly, at LinkedIn, whose official statement persists in using the seemingly harmless phrase "some passwords", several factors suggest that the list of 6.5 million SHA1 hashes posted online may exclude simple passwords that have already been cracked. A blog post entitled LinkedIn vs password cracking gives an excellent overview of the contemporary tools and techniques used to crack passwords.
The concrete effects of this particular password leak are not yet clear. The publicly distributed lists do not include user names or email addresses. It would, however, seem reasonable to assume that whoever stole the passwords also has, and is using, this information. Last month Last.fm admitted to having received several reports of spamming involving user data. Since identical spam is sometimes sent to email addresses from the LinkedIn and Last.fm leaks, it is more than likely that both databases have fallen into the same hands.
There is also a first indication as to why Last.fm failed to implement rudimentary security measures to protect its users' passwords. According to someone claiming to be a former system architect at the company, design weaknesses in the music service's mobile API architecture were responsible for the, by today's standards, weak encryption. The technique employed uses the password and client-side user name to calculate an access key. For the server to check this, it needs to store the password, which is secured only with MD5 hashes. The API was developed 9 years ago, and appears not to have been updated since. It's going to be interesting to see what comes to light regarding the reasons for the sloppiness at these companies.
And one amusing detail â although eHarmony implores its users to use strong passwords including both upper and lower case letters, it saves the passwords in all upper case, thereby weakening its already weak security further. The hypocritical concern expressed by these companies has been covered in an editorial from The H Security: "Comment: LinkedIn and its password problems".
(Ingo Macherius / crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








