PIN skimming possible with chip cards
 At the CanSecWest security conference held in Vancouver last week, four security researchers demonstrated the practicability of chip card skimming attacks – both with an insecure class of chip (SDA) and with a class that has been considered secure (DDA). EC and credit cards chipped according to EMV specifications are designed to hamper "skimming", an attack method which involves intercepting a user's card and PIN data.
At the CanSecWest security conference held in Vancouver last week, four security researchers demonstrated the practicability of chip card skimming attacks – both with an insecure class of chip (SDA) and with a class that has been considered secure (DDA). EC and credit cards chipped according to EMV specifications are designed to hamper "skimming", an attack method which involves intercepting a user's card and PIN data.
Skimming attacks aren't an altogether new idea and can also be carried out via such devices as keyboard attachments. In their presentation, entitled "Credit Card skimming and PIN harvesting in an EMV world" ![]() , however, the four researchers describe how a flat circuit board inside the card slot can be used to intercept and manipulate the communication between terminal and chip in order to obtain a user's PIN. A circuit board is far more discrete than a wobbly, glued-on attachment.
, however, the four researchers describe how a flat circuit board inside the card slot can be used to intercept and manipulate the communication between terminal and chip in order to obtain a user's PIN. A circuit board is far more discrete than a wobbly, glued-on attachment.
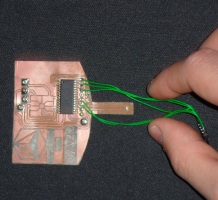
![]() Small, flat and discrete: the EMV skimmer in a terminal's card slot is designed not to attract any attention.
The trick used by Andrea Barisani and Daniele Bianco from Inversepath, as well as Adam Laurie and Zac Franken from Aperturelabs, involved signalling to the terminal a list of the card's approved verification methods (CVM list) that includes transmitting the PIN to the card in plain text (Plaintext PIN verification performed by ICC). Although the PIN is only transmitted to the card in the terminal's offline mode – in online mode, the terminal will send the PIN to the central server for verification –, the researchers managed to force an offline plain text verification by manipulating the communication between card and terminal. The circuit board in the card slot allowed them to harvest the PIN.
Small, flat and discrete: the EMV skimmer in a terminal's card slot is designed not to attract any attention.
The trick used by Andrea Barisani and Daniele Bianco from Inversepath, as well as Adam Laurie and Zac Franken from Aperturelabs, involved signalling to the terminal a list of the card's approved verification methods (CVM list) that includes transmitting the PIN to the card in plain text (Plaintext PIN verification performed by ICC). Although the PIN is only transmitted to the card in the terminal's offline mode – in online mode, the terminal will send the PIN to the central server for verification –, the researchers managed to force an offline plain text verification by manipulating the communication between card and terminal. The circuit board in the card slot allowed them to harvest the PIN.
In this context, it appears to be irrelevant whether the card's chip is of the inexpensive type without built-in cryptography (SDA) or the expensive type offering Dynamic Data Authentication (DDA) that has been considered secure up until now. However, in order to use the harvested PIN, the skimmer must either steal the customer's card or read out the card's magnetic strip and clone the card. The latter solution will only work with cards that aren't protected via an "iCVV" code which will signal to the card issuer that the magnetic strip has been tampered with.
Daniele Bianco explained: "The real problem with EMV is that the method's apparent security shifts the burden of proof to the customer. Customers are accused of having been careless with their PINs." According to Bianco, the problem affects all types of EMV implementations. "As the problem is rooted in the protocol specification, the hole won't be easy to fix."
That there are fundamental issues with the protocol specification has, in fact, been known to card issuers and banks for more than five years. At that time, researchers at the University of Cambridge had already described a skimming attack on SDA cards. Little has changed since then. About a year ago, the same UK researchers demonstrated a method which allows EMV to be bypassed in such a way that EC and credit cards seemingly accept arbitrary PINs. However, this type of manipulation could be exposed afterwards.
See also:
- UK court sentences Chip & PIN skimmers, a report from The H.
- Credit card skimming attacks on pay-at-the-pump petrol stations, a report from The H.
- Hacker extracts crypto key from TPM chip, a report from The H.
(Marc Heuse / crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








