Microsoft report: Users responsible for half of all infections
![]() Almost half the time, the main security vulnerability is sitting in front of the screen.
Almost half the time, the main security vulnerability is sitting in front of the screen.
Source: Microsoft
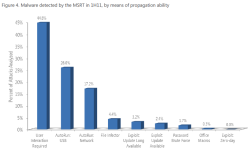
In its latest security report, Microsoft finds that only 5.6 per cent of all infections with malicious software are the result of security holes. Almost half the time (45 per cent), users infect their computers by launching malicious software themselves.
Infected USB sticks are behind an impressive 26 per cent of all attacks. This vulnerability is made possible by the USB autostart function, which was only included in Windows up to Vista; in February, Microsoft disabled it with an update. Infected network shares are behind 17.2 per cent of all attacks, with contaminants spreading by infecting other files 4.4 per cent of the time.
Brute force attacks on passwords and manipulation of Office macros are relatively negligible in spreading viruses at 1.7 and 0.3 per cent, respectively. It is the first time that Microsoft has analysed how viruses are disseminated in its report. Up to now, a lot of experts had assumed that vulnerabilities play a much greater role in computer infections.
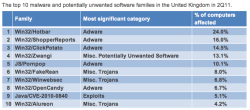
The number of infected computers in the UK dropped though. In the third quarter of 2010, 7.4 in every 1,000 computers investigated in the UK were infected, a figure that dropped to only 5.2 infected computers in the second quarter of this year. The UK performs reasonably well in this respect compared to the global average of 9.8 computers. British computer users mainly fall prey to adware (49.1 per cent). 31.9 per cent came into contact with "miscellaneous trojans", a rise of almost 5 percentage points, and 27.9 per cent came into contact with "potentially unwanted software".
![]() The main contaminant in the UK is adware
The main contaminant in the UK is adware
Source: Microsoft
In the UK, in the previous report, Microsoft found that the JavaScript-based adware JS/Pornpop, which specialises in pop-up windows containing porn advertising, was the most common, but this has fallen to fifth place. The top position is now taken by Win32/HotBar, a toolbar which delivers targeted adverts and monitors the user's activity, followed by the similar Win32/ShopperReports and Win32/ClickPotato. Fourth place went to Win32/Zwangi, which modifies browser settings in the background to send users to particular sites.
Fake anti-virus software leads the trojans in the top ten: the sixth place is taken Win32/FakeRean, with Alureon coming in tenth place; in Germany, Alureon is the only trojan in the top ten. While it was still there in the second half of 2010, ZeuS has now disappeared from the top ten altogether, as has Conficker.
The data analysed was collected in 100 countries from more than 600 million systems on which Microsoft's Malicious Software Removal Tool is used. Microsoft offers instructions![]() that IT experts can download to help identify and remove malicious software on their systems.
that IT experts can download to help identify and remove malicious software on their systems.
(djwm)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








