Microsoft Outlook also caught in the URI trap
According to an advisory by security service provider Secunia, Outlook Express and Outlook 2000 are also affected by the Windows URI problem. Not only Firefox, Skype, Adobe Reader, Miranda, mIRC and Netscape as previously reported, but also Microsoft applications might be exploited to launch arbitrary programs on a user’s system by clicking a malicious URL. As yet, Microsoft has not seen the need to provide a patch to eliminate the problem at its source, i.e., Windows, and has denied any related vulnerability in Microsoft products.
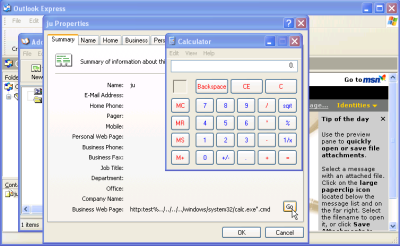
The cause of the problem is Windows’ inconsistent behaviour when opening certain URLs containing invalid strings. Whereas Windows XP with Internet Explorer 6 launches the appropriate URL handler to deal with these URLs – for instance, Outlook Express in case of mailto: URLs – it can execute an arbitrary application if Internet Explorer 7 is installed, e.g. the calculator in harmless demos. Windows Vista, on the other hand, merely produces an error message when the same URLs are opened. Security service provider Secunia was [ticker:uk_93455 one of the first] to determine that Windows, rather than Firefox, is the real cause of the problem.
Many applications, including Outlook Express and Outlook 2000, simply pass URLs for which they do not consider themselves responsible to the operating system. A short test performed by heise Security has shown that clicking ‘Go’ on a special entry in the address book of Outlook Express launches the calculator without any prompt to the user. Under Windows XP with IE7 this may allow attackers to inject malicious code, e.g. spyware, onto a system via specially crafted VCards.
Only yesterday, Adobe warned of a similar problem in Adobe Reader/Acrobat and has announced a patch by the end of October. Although Firefox and Skype have already released updates to protect their users, mIRC, Netscape and Miranda and propably others are still affected. The announcement that Outlook, too, is caught in the URI trap, increases hopes that Microsoft will finally accept its responsibility for addressing the problem, and will take steps to make the behaviour of Windows more predictable. Thomas Kristensen, CTO of Secunia pointed out: "We hope that Microsoft now chooses the right path and creates a general fix for Windows / IE7 rather than start patching all their own applications and ask third party vendors to do the same."
- Microsoft Windows URI Handling Command Execution Vulnerability security advisory by Secunia
- Adobe warns of URI problems report by heise Security
- URI problem also affects Acrobat Reader and Netscape report by heise Security
(ju)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








