HeapLocker tool for Windows blocks injected code
The HeapLocker tool for Windows is designed to make it more difficult for attackers to execute code that has been injected via security holes. The tool was developed by Didier Stevens, who had previously gained a reputation as a PDF security specialist.
HeapLocker in particular provides protection against an attack type called heap spraying, which involves attackers repeatedly injecting code into an application's heap to ensure they can jump to it. For this purpose, attackers write long sequences of no-operation instructions (NOPs), followed by the actual malware, into memory. Even an untargeted jump to the heap is then very likely to end up on such an NOP slide and eventually start the code.
HeapLocker is designed to pre-allocate the heap of a process to ensure that there is no room for spraying. The tool also monitors how much of the virtual heap memory is in use – heap spraying uses up immense amounts of it. Once a customisable limit is reached, the tool will issue an alert and stop the process. HeapLocker can reportedly also detect NOP slides and offer to terminate a program in case of an attack.
As a last line of defence, the tool can recognise character strings that are typically found in exploits – although this currently only works with specially crafted PDF documents. When tested by our associates at heise Security, HeapLocker blocked an exploit for Adobe Reader after detecting a malicious signature.
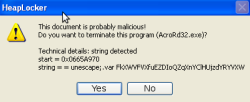
![]() Here, dubious JavaScripts which produce unescaped character strings have triggered HeapLocker into action.
Stevens says he has tested HeapLocker with Adobe Reader 8.1.2 and 9.4.3 as well as Foxit Reader 4.1, Excel 2003, Firefox 3.6.3 and Internet Explorer 8 under Windows XP SP3. In terms of long-term stability, however, the developer has only tested Adobe Reader.
Here, dubious JavaScripts which produce unescaped character strings have triggered HeapLocker into action.
Stevens says he has tested HeapLocker with Adobe Reader 8.1.2 and 9.4.3 as well as Foxit Reader 4.1, Excel 2003, Firefox 3.6.3 and Internet Explorer 8 under Windows XP SP3. In terms of long-term stability, however, the developer has only tested Adobe Reader.
With these features, HeapLocker basically has the potential to compete with Microsoft's Enhanced Mitigation Experience Toolkit. However, the tool in its current form is anything but user friendly. To activate HeapLocker, users need to load the heaplocker.dll file into the target application via the import table. This requires further tools such as an editor for PE headers to edit, for instance, the AcroRd32.exe file.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








