Hackers turn remote maintenance tool into trojan
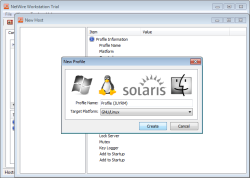
![]() NetWire during generation of a Linux host
Hackers are using remote maintenance tool NetWire, which can be used to monitor computers running Windows, Mac OS X, Linux and Solaris, as a trojan. Anti-virus software companies have responded by identifying the program as malware.
NetWire during generation of a Linux host
Hackers are using remote maintenance tool NetWire, which can be used to monitor computers running Windows, Mac OS X, Linux and Solaris, as a trojan. Anti-virus software companies have responded by identifying the program as malware.
World Wired Labs describes its NetWire product as an extended remote maintenance application. The host application runs under Windows, various versions of Linux, Mac OS X and Solaris, while the "administrators workstation" client, from where a host can be controlled, runs under Windows only. The basic version costs $65, the Pro version, which can be extended using add-ons, is priced at $105. Prices for the Advanced version are available on request.
So far, so simple. But the line in the price list that says "undetected" hints that there's more to this than meets the eye – this amounts to a promise that the Windows version of NetWire Advanced will not be detected by anti-virus software. We find ourselves in a grey area.
The company calls NetWire a reliable tool for remote maintenance of business infrastructure, which is able to cross operating system barriers. The connection between the client and server is protected using AES encryption and is limited to a single TCP port. But the company also advertises "special remote access requirements", from monitoring to parental supervision. In this case, NetWire monitors all processes and even generates screenshots.
The program is advertised in a very different light on hacker forums. Here, the emphasis is on NetWire's ability to use reverse proxying to pass through any firewall or router, its ability to read browser passwords from any browser and the fact that its keylogger does not require administrator privileges. Extensions for sniffing out TrueCrypt passwords and logging instant messaging conversations are also in the pipeline. Seen from this angle, the remote maintenance tool starts to look a lot like a trojan toolkit.
The company behind the product is not at all happy about its product finding its way into some of the darker corners of the web. Each time a remote maintenance host is generated, NetWire displays a disclaimer which requires the user to confirm that he or she will not use NetWire to gain unauthorised access to another computer or to perform other illegal activities.
The hacker who had been promoting NetWire as a multi-platform trojan was quickly ejected from World Wired Labs' affiliate programme. That has not, however, stopped other hackers from offering special "crypters", which claim to be able to hide NetWire executables from anti-virus programs, on private hacking forums.
So it's no great surprise that the remote maintenance program now finds itself in the firing line from anti-virus software companies. Dr. Web describes NetWire as a password stealer and lists it as "BackDoor.Wirenet.1". Other companies have dubbed it "TrojanSpy", "NetWired" and "NetWeird". According to VirusTotal, the Standard version of NetWire for Windows is currently detected by 16 anti-virus programs, the Linux version by 6, the Solaris version by 4, and the Mac version by 9 scan engines. Bizarrely, the Windows client is detected more frequently than the hosts, with 26 of 42 programs raising the alarm. The toolkit is therefore viewed as being more malicious than its compiled code.
(djwm)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








