Google's Jarlsberg server: full of holes like the cheese
![]() Google says "Jarlsberg is the cheesiest application on the web"
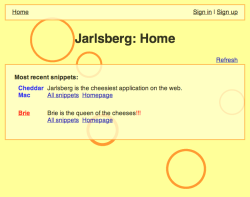
Google's online tutorial for web developers includes a server which demonstrates typical vulnerabilities for them to virtually exploit. The tutorial consists of two elements: an intentionally unsafe mini-blog web application – Jarlsberg (named after the Norwegian cheese) and a guide on how to find vulnerabilities in the application.
Google says "Jarlsberg is the cheesiest application on the web"
Google's online tutorial for web developers includes a server which demonstrates typical vulnerabilities for them to virtually exploit. The tutorial consists of two elements: an intentionally unsafe mini-blog web application – Jarlsberg (named after the Norwegian cheese) and a guide on how to find vulnerabilities in the application.
The Google Code University's guide includes sections on cross-site scripting, path traversal, code execution and denial of service. It then challenges the student to exploit the various vulnerabilities on the Jarlsberg server, providing some hints along the way. For those who do not discover the solutions, each section ends with answers and a suggestions on how the student might improve their technique.
The course is available on line, and Google's Jarlsberg server is available on Google's App Engine, or it can be downloaded and run locally. No analysis of the source code is necessary to find the vulnerabilities.
Not all the vulnerabilities can be exploited using the browser; for example, to obtain a particular file through a path traversal download, the student will need to use a command line tool called curl. This is because many browsers pre-translate a URL such as http://jarlsberg.appspot.com/305378746796/../secret.txt into http://jarlsberg.appspot.com/secret.txt and therefore are unable to exploit the hole.
(djwm)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








