Flashback: two thirds of all infected Macs run Snow Leopard

![]() Clearly discernible: the malware seems to be particularly comfortable on Snow Leopard (Darwin kernel versions 10.x), but it also likes Leopard (kernel versions 9.x), which is completely defenseless against the trojan
Clearly discernible: the malware seems to be particularly comfortable on Snow Leopard (Darwin kernel versions 10.x), but it also likes Leopard (kernel versions 9.x), which is completely defenseless against the trojan
Source: Dr.Web
According to a report by Russian IT security firm Dr.Web, the Flashback malware has made itself particularly comfortable on systems running Mac OS X 10.6 Snow Leopard. The anti-virus specialist and discoverer of the currently active Flashback variant has recorded and evaluated the botnet's communications.
Dr.Web says that Apple computers running the predecessor to 10.7 Lion, 10.6 Snow Leopard, are particularly affected. Almost 63% of infected Macs run Snow Leopard, and another quarter use Mac OS X 10.5 Leopard. Only 11% of systems infected with the Flashback botnet are unpatched Lion machines.
Leopard users currently have no official way of protecting themselves against the trojan, because Apple only provides security updates for Snow Leopard and Lion. Making matters even worse, the Flashback malware removal tool only works under Mac OS X 10.7.
One of the likely reasons why significantly fewer Lion systems are affected is that Java is no longer a default component of the latest Mac operating system and must be installed manually. Apple's future plan is to completely abandon its own Java development and leave it to Oracle, which published its first sponsored Java release for Mac OS X last week.
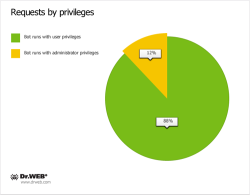
![]() Only few users have granted administrator privileges to the Flashback trojan
Only few users have granted administrator privileges to the Flashback trojan
Source: Dr.Web
However, it appears that Mac users tend to be more suspicious when being asked for their admin password – Flashback must make do without root on 88% of infected computers. The trojan initially asks users to enter an administrator name and password.
See also:
- Flashback numbers not going down - still over half a million, a report from The H.
- Worth Reading: An analysis of the Flashback/Flashfake trojan, a report from The H.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








