Flash Player as a spy system
![]() Adobe's online flash settings vulnerable to manipulation
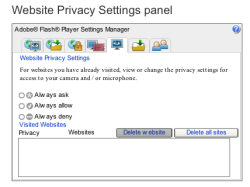
If a forged certificate is accepted when accessing the Flash Player's Settings Manager, which is available exclusively online, attackers can potentially manipulate the player's website privacy settings. This allows a web page to access a computer's web cams and microphones and remotely turn the computer into a covert listening device or surveillance camera.
Adobe's online flash settings vulnerable to manipulation
If a forged certificate is accepted when accessing the Flash Player's Settings Manager, which is available exclusively online, attackers can potentially manipulate the player's website privacy settings. This allows a web page to access a computer's web cams and microphones and remotely turn the computer into a covert listening device or surveillance camera.
At the "Meta Rhein Main Chaos Days 111b" (German language link), Fraunhofer SIT employee Alexander Klink presented![]() a scenario in which he used a man-in-the-middle attack (MiTM) to intercept the communication with Adobe's Settings Manager. The Settings Manager itself is a simple Flash applet, and the Adobe pages load it into the browser as an SWF file via HTTPS – a fixed link to it is encoded into the browser.
a scenario in which he used a man-in-the-middle attack (MiTM) to intercept the communication with Adobe's Settings Manager. The Settings Manager itself is a simple Flash applet, and the Adobe pages load it into the browser as an SWF file via HTTPS – a fixed link to it is encoded into the browser.
However, the MiTM attack allows attackers to inject a specially crafted applet which, to put it simply, manipulates the Flash cookies (Local Shared Objects, LSOs) on the victim's computer in such a way that the computer's web cam and microphone become accessible to arbitrary domains – by default, no domain has access to these components. This, in turn, allows images and audio to be transmitted to the attacker's server via RTMP streaming.
While attackers need their potential victims to co-operate and accept a forged certificate in order to hack the SSL connection, an error when accessing one of Adobe's Macromedia pages is unlikely to cause much suspicion. Adobe has been informed about the problem and is considering whether to release a new GUI for the Settings Manager. Klink suggests that a warning be displayed when a user accesses certain APIs of external pages. Another alternative is to set the "AVHardwareDisable = 1" option in the mms.cfg configuration file completely disables Flash Player's access to audio and video hardware. The location of this file is revealed in a tech note by Adobe.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








