First vulnerability in Vista's Windows Mail
The successor to Outlook Express perpetuates its predecessor's dubious reputation in matters of security. Just a few months after its official release, the first significant security problem has been uncovered. Under certain circumstances, simply clicking on a link in an email can cause a program to be launched on the local computer.
A hacker going by the pseudonym Kingcope has reported on a security mailing list that this can be achieved by simply embedding a link to a local program in an email. If a directory with the same name as the executable program exists, the program will be executed by Windows Mail without requiring any confirmation when the user clicks on the link. A brief test at heise Security confirmed this. After creating a folder called calc in C:\Windows\System32\, clicking on a link to c:/windows/system32/calc? launched the calculator without any further user interaction.
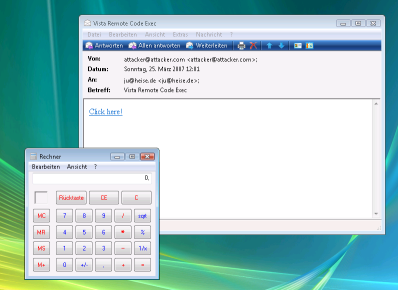
![]() Under certain circumstances a click on a link can execute a program in Windows Mail
There is currently no real attack scenario to exploit this, and so the concrete danger is fairly low. Kingcope has listed two Windows programs, winrm and migwiz, for which the required directory already exists. But he admits that it was not possible to pass parameters to the programs, which significantly reduces the potential for targeted activities. But it is disquieting that merely clicking on a straightforward URL in an email can be sufficient to launch a local program without any user confirmation. Many dangerous vulnerabilities in Outlook Express and Internet Explorer initially appeared to be similarly innocuous. And Microsoft will now be judged against the grandiose promises it made with regard to the security of Vista.
Under certain circumstances a click on a link can execute a program in Windows Mail
There is currently no real attack scenario to exploit this, and so the concrete danger is fairly low. Kingcope has listed two Windows programs, winrm and migwiz, for which the required directory already exists. But he admits that it was not possible to pass parameters to the programs, which significantly reduces the potential for targeted activities. But it is disquieting that merely clicking on a straightforward URL in an email can be sufficient to launch a local program without any user confirmation. Many dangerous vulnerabilities in Outlook Express and Internet Explorer initially appeared to be similarly innocuous. And Microsoft will now be judged against the grandiose promises it made with regard to the security of Vista.
- Microsoft Windows Vista - Windows Mail Client Side Code Execution Vulnerability security bulletin from Kingcope
(ju)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








