EMET exploit mitigation tool reports the cause of a crash
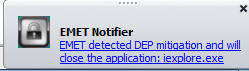
When EMET terminates a process for security reasons, an alert window is displayed above the Windows system tray
Source: Microsoft
Microsoft's Enhanced Mitigation Experience Toolkit (EMET) now notifies users when a process has been stopped (crashed) because a protective mechanism was activated by the hardening tool. The new feature was introduced with the recent 3.0 release of EMET, which is also designed to be easier to use in enterprise environments.
When the alert window is displayed above the system tray area, this alerts users that an attacker may have tried to exploit a vulnerability in the named process – but it isn't hard evidence of an actual attack. EMET will also write these and other alerts, information and errors into the Windows Application log.
Administrators can now deploy the tool across a network using Group Policies or the System Center Configuration Manager (SCCM). EMET 3.0 can import and export "Protection Profiles" with customised settings for common Microsoft and third-party applications, and three default configuration profiles are included. The company says that EMET has also been tested under the Windows 8 Consumer Preview.
EMET offers protective mitigation features for arbitrary applications without requiring access to their source code. On several occasions, Microsoft has published instructions how to use EMET to mitigate the potential effects of new zero-day exploits; an overview of how EMET can be used to protect programs against attacks is explained in "Damage limitation: Mitigating exploits with Microsoft's EMET" from The H Security. EMET 3.0 is available from Microsoft's Download Center, and supports Windows XP SP3 or later, Vista SP1 or later, or Windows 7, as well as Server 2003 SP1 and above, and Server 2008.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








