Crypto tool predicts password cracking time
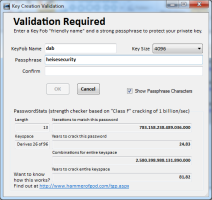
![]() A brute-force attack on this password would take almost 25 years, but a dictionary attack might be successful sooner.
Instead of indicating password quality via coloured bars, the Windows crypto tool Thor's Godly Privacy (TGP) informs users about the estimated time required for a successful brute-force attack on the chosen password. TGP calculates the time from the number of iterations a brute-force tool would need to arrive at the correct character combination.
A brute-force attack on this password would take almost 25 years, but a dictionary attack might be successful sooner.
Instead of indicating password quality via coloured bars, the Windows crypto tool Thor's Godly Privacy (TGP) informs users about the estimated time required for a successful brute-force attack on the chosen password. TGP calculates the time from the number of iterations a brute-force tool would need to arrive at the correct character combination.
The calculation is based on a Class F attack with a throughput of 1 billion passwords per second and a key space of 96 that contains all lower and upper case letters as well as all numbers and special characters, brackets etc (961 + 962 + 963 + 964 + ...). However, TGP not only returns the time required for trying out the entire key space, it also gives an estimated time for the specific password in question; 10 × the letter A differs considerably from 10 tildes.
This way, the tool impressively demonstrates that the length of a password is more important for its resilience than the complexity – if we disregard simple long passwords such as "Hippopotomonstrosesquipedaliophobia" that can be cracked via dictionary attacks. Developer Timothy "Thor" Mullen thinks that the displayed information gives users a better idea than green and red bars or quality indicators such as "good", "medium" or "bad".
The "PasswordStrength" checker is part of TGP's key generation, which is used for encrypting files. TGP ("encryption for the cloud") embeds base64-encoded files in an XML form which is easy to publish on a web page. Those who want to try out the PasswordStrength checker but don't want to install the complete crypto tool can use the online version. However, no passwords intended for later use should be entered there.
Recently, a password recommendation by Bitkom sparked a controversy. Bitkom recommended that company employees should regularly change their passwords, and that there should be guidelines for a password's minimum length and level of complexity.
(crve)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








