AusCERT on the Internet Census: It's not the fault of "stupid users"

When three careless default settings are present at the same time, criminals often enjoy easy access to devices and industrial control systems. This is what the Australian Computer Response Team (AusCERT) found in one of its most recent analyses of previously undisclosed data relating to the Internet Census 2012. For the analysis, which was presented at the AusCERT conference last week, the creator of the census gave AusCERT nine terabytes of data, including information on 1.2 million identifiable devices that could be infected with the Carna botnet, which made it possible to scan all of the IPv4 address space.
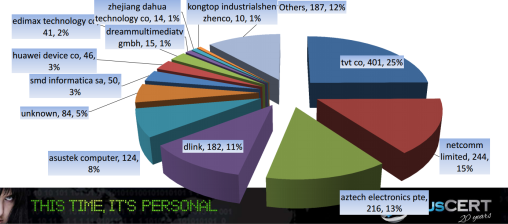
![]() AusCERT evaluated the affected manufacturers on a national and international level
AusCERT evaluated the affected manufacturers on a national and international level
Source: AusCERT
AusCERT found that Carna exploits careless default configurations. The botnet infected devices are directly accessible through the internet, provide telnet access on port 23 without a firewall, and use default login data such as admin:admin, admin:password or root:password. It was easy to identify the devices in question from the output of the ifconfig command. AusCERT emphasised the fact that the devices are this vulnerable is down to the manufacturers and that it was not the fault of "stupid" users.
Users often have little opportunity to manually change their devices' default settings, argues AusCERT. Backdoors are often hardcoded deliberately by the manufacturers, log-in data can't be changed, or users aren't even informed that a device has an active internet connection, said AusCERT. In addition, some devices require a publicly reachable IP for their full range of features to be accessible.
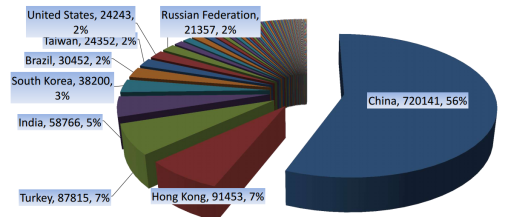
![]() Insufficiently protected devices lurk especially in China
Insufficiently protected devices lurk especially in China
Source: AusCERT
Apparently, only about 1,614 of the around 1.2 million identified devices are located in Australia, and 25 per cent of all affected devices in Australia were manufactured by TVT Co. The experts said that 15 per cent were NetComm Limited devices, 13 per cent were made by Aztech Electronics Pte Ltd, and 11 per cent by D-Link.
The majority of insufficiently protected devices were located in China, followed by Turkey and India. The AusCERT noted that, to close the security holes on a global scale, the team has passed on its research results to all countries and associated CERTs where more than ten thousand devices are affected. In all, information was sent out to a total of 22 countries. AusCERT says that the majority of security holes could be alleviated by simply closing port 23. The Carna botnet was developed in such a way that it can often be removed through hardware resets or reboots.
(fab)








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








