
Systematic safety
The other concept is based on the idea that users derive their own service-specific variations from an "uncrackable" basic password. However, this also has its disadvantages – not the least of them being the risk that somebody might recognise the user's pattern and gain the ability to jump from one account to the next.
Therefore, you should come up with your own method of using a template to derive a unique password for an online service, and don't use what we're presenting below verbatim. For web sites, the domain name is an obvious choice on which to base your variations. For example, insert the domain name's first and third letters as each password's third-but-last and last characters. Finally, put the number of characters in the second position.
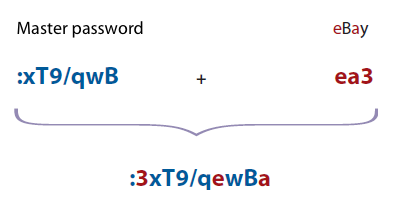
This gives you a good chance of being able to recreate your forgotten access password even after a few months of eBay abstinence. Should some criminals acquire this password, for example by breaking into eBay, there is little danger that they will be able to derive your Amazon password from it.
Chances are also slim that a cracker might resolve your eleven-character password after breaking into eBay. First of all, eBay hopefully uses more diligence than LinkedIn. And eleven quasi-random characters will withstand GPU attacks on SHA1 beyond the limits of a cracker's patience. The recently introduced 25 GPU cluster would need over 135 years.
That someone will detect your variation pattern with their naked eye is also rather unlikely. Only if crackers have accessed plain text versions of several of your passwords and sent them through their variation machinery is there a risk that your method will be discovered.
Three password rules: lie, cheat and falsify
Lie: Backup questions for password resets are backdoors that are often used for intrusions. "Your first car" or "your mother's maiden name" – such information can easily be researched by others, particularly if a potential intruder has targeted you specifically.
Cheat: If you use any numbers in your passwords, for example a year or the number of characters of a domain name: cheat when you do so. Always add three or deduct one from the actual value.
Falsify: If you use a template when creating your password – a silly phrase, a song lyric or a quote: Always falsify the original to some degree.
Make sure you understand that your passwords are valuable. Don't waste them on sites where there is a high risk that they will be handled inappropriately and stored as MD5 or SHA1 hashes, or even in plain text. Sadly, users don't tend to have a way of knowing. Therefore, use your full master password only on truly trustworthy sites. For all other occasions you can use a lean basic version that could, for example, involve removing any numbers and special characters (xTqwB) and using a modified variation rule.
Throw-away passwords
On various forums that I don't fully trust, I will use a few throw-away passwords that aren't totally obvious, but I'm aware that they are crackable if someone puts their mind to it. Let them do so – I only use these passwords where no harm whatsoever can be done.
Finally, for passwords that are particularly sensitive and exposed, I take care that they are designed to be particularly secure and unique. This includes the passphrase of my GPG key, my email password, of course, my online banking credentials, as well as anything where offline attacks must generally be expected, such as Truecrypt containers that are stored in a cloud. If I have any doubts I will resort to my safe note for this, as I haven't yet heard of any technique that would allow a trojan to bridge the air gap between my PC or smartphone and the written note in my desk at home.








![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)








