Fully virtual networks
Sven Ahnert
Network configuration in virtual machines
Virtual machines like VMware or Microsoft's Virtual Server can be used to simulate networks or securely run servers in a sandbox environment. Detailed knowledge of the internal procedures and various scattered options is essential to do this properly
Virtual networks offer more configuration options than physically wired ones, and as a result raise more questions: as platforms, productive virtual servers have to be addressable on all LAN levels, if possible with redundant connections. In a test environment, on the other hand, providing security for network segments is the primary task, ideally behind a firewall. Developers want to access their virtual SQL servers while away from the office, and their virtual machines (VM) should be able to use the laptop's UMTS or ISDN connections. Several solutions are available to meet these requirements.
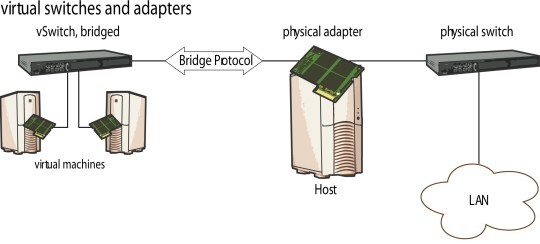
![]() Switches and network adapters all have their counterparts in VMWare...
Switches and network adapters all have their counterparts in VMWare...
This article describes the concepts behind virtual networks, from virtual switches to MAC addresses, and offers practical tips. We will use version 1 of VMware server as an example, because it offers comprehensive network options and is freely available to anyone. What we will discuss also applies to newer versions and to the VMware workstation. Where required, we will discuss the particular characteristics of VMware's commercial ESX server. The network setup of Microsoft's free Virtual Server/PC is slightly different.
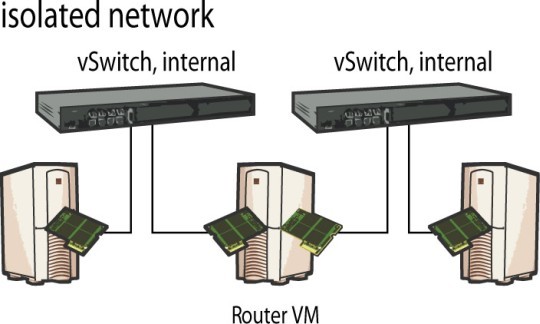
![]() ...so do networks isolated via routers.
...so do networks isolated via routers.
All virtual machines share a similar basic structure, and almost all of the components found in a physical network also appear in the virtual world.




![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/6/7/2/comingin310_4_kicker-4977194bfb0de0d7.png)

![Kernel Log: Coming in 3.10 (Part 3) [--] Infrastructure](/imgs/43/1/0/4/2/3/2/3/comingin310_3_kicker-151cd7b9e9660f05.png)












